Obscure Computing
Obscure ComputingObscure ComputingObscure Computing

Obscure Computing represents the work, experience, and professional perspective of David Tuman, a cybersecurity professional and technical leader with more than 20 years of military and cybersecurity experience operating in complex, mission-critical environments.
David’s career has focused on building and supporting secure systems, leading technical teams, developing cyber capabilities, and solving real-world security problems. His experience spans cyber operations, system security, infrastructure, technical training, and workforce development, with a consistent focus on mission execution, accountability, and measurable improvement.
What sets his approach apart is the balance between technical depth, leadership and innovation. Whether developing tools, designing training pipelines, improving operational processes, or guiding teams through difficult technical challenges, the objective remains the same: build capability, reduce risk, and deliver outcomes that matter.

https://obscurecomputing.com/digital-fortress-opera
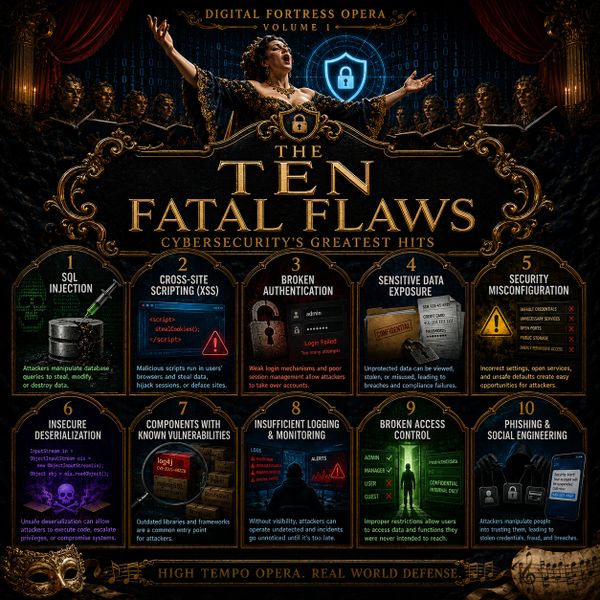
David is currently supporting Digital Fortress Opera – Volume 1, an energetic and engaging cybersecurity music and education project that turns common security failures into memorable lessons for defenders, leaders, and learners.
Each track explores a major cybersecurity risk, from SQL injection and cross-site scripting to phishing, ransomware, access control, logging, monitoring, and secure configuration. Obscure Computing provides supporting analysis for each song, translating the music into practical cybersecurity lessons and leadership takeaways.
Explore the album guide and track-by-track analysis.
Video Link Below:
https://obscurecomputing.com/ten-fatal-flaws-1
The first track, “Ten Fatal Flaws,” introduces the major security failures explored throughout Digital Fortress Opera – Volume 1. The song moves through common weaknesses such as injection, cross-site scripting, broken authentication, exposed data, misconfiguration, vulnerable components, insufficient monitoring, broken access control, phishing, and ransomware. The supporting analysis explains why these issues continue to appear in modern environments and how leaders can reduce risk through secure design, disciplined operations, visibility, accountability, and a security-aware workforce.
Video Link Below:
We use cookies to analyze website traffic and optimize your website experience. By accepting our use of cookies, your data will be aggregated with all other user data.